Distributed Denial of Secrets is a transparency collective with an unusual mission in the age of PeakTwitter: “avoid political, corporate or personal leanings.” They say they don’t do hacking but they have posted the result of a hack a trove of 230,000 emails from Russia’s Ministry of Culture. DDOSecrets lives on the so-called Dark Web,...
HAPPENING NOW:
Inside the Discord Leak: U.S. Air Force Loves War Gamers Like Teixeira
British Intelligence Privately Says Israel Has Nuclear Weapons But Won’t Admit it Publicly
Mexican President Accuses Pentagon of Spying, Vows to Restrict Military Information
Daniel Ellsberg Week Honors Pentagon Whistleblower
How Twitter Became a Propaganda Tool of U.S. Central Command
Interview With the Father of a Palestinian Fighter Assassinated by Israeli Special Forces
Chinese Police Station in New York Is Part of a Vast Influence Operation
Catch-22 at Guantanamo, or How Due Process Got Undone
Wagner Group Leader Calls for End to Russia’s ‘Special Military Operation’
Once Ridiculed, the ‘October Surprise’ Deal Between Reagan and Iran Is Now Confirmed
Two Senators Allege ‘Secret’ CIA spying on Unwitting Americans
UK Spy Agency Says AI Chatbots Pose a Security Threat
How Aerial Surveillance Has Evolved Over the Past 200 Years
Wagner Mercenary Chief Says He Ran Russian Information War
Iranians Outraged After Shah-Era Secret-Police Official Attends U.S. Rally
Israeli-led Disinformation Team Meddled in Dozens of Elections
Director of National Intelligence Barred From Reporting on Domestic Extremists in U.S. Armed Forces
Iranian Intelligence Official Says China in Line to Buy Tehran’s Drones
Former Mossad Chief Urges Compromise on Judicial Shakeup
Tag: hacking
DDoSecrets Publishes the Email From Russia’s Ministry of Culture
Six GRU Officers Charged With Cyber Attacks on Ukraine, South Korea, and French Elections
From the U.S. Department of Justice: These GRU hackers and their co-conspirators engaged in computer intrusions and attacks intended to support Russian government efforts to undermine, retaliate against, or otherwise destabilize: (1) Ukraine; (2) Georgia; (3) elections in France; (4) efforts to hold Russia accountable for its use of a weapons-grade nerve agent, Novichok, on...
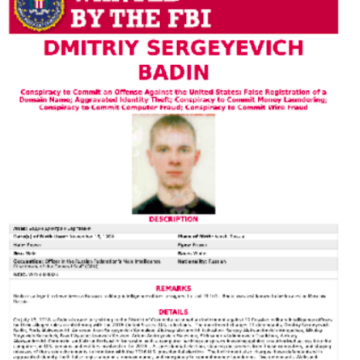
Who Is Dmitry Badin, the GRU Hacker Indicted By Germany For Hacking the Bundestag?
From Bellingcat, a deep dive on a GRU hacker, involved in multiple hacking operations. The story underscores and illuminates the fact the GRU is involved in operations against the German parliament, the Bundestag, as well as international organizations such as The Organisation for the Prohibition of Chemical Weapons and the World Anti-Doping Agency. It is...
Maxim Yakubets, Russia’s Top Hacker, Has Ties to Russia’s FSB
This story comes, not from Western intelligence agencies (which have a vested interest in elevating the threat of Russia) but from the independent Russian media, which has a vested interest in exposing how the country’s opaque authoritarian regime functions. Here investigative journalist Liliya Yapparova from Meduza explores the hacking collective known as Evil Corp and...
Four Members of Chinese Military Charged With 2017 Hack at Equifax
From The Washington Post: In a nine-count indictment filed in federal court in Atlanta, federal prosecutors alleged that four members of the People’s Liberation Army hacked into Equifax’s systems, stealing the personal data as well as company trade secrets. In a statement announcing the case, Attorney General William P. Barr called their efforts “a deliberate...